How a solo CISO can start NIS 2 and ISO 27001 without help (and actually measure the work)
A practical ISO 27001 and NIS 2 readiness playbook for small security teams. Day-by-day, week-by-week. From zero to certified in 4-6 months without Big 4 consultants.
If you just inherited security for a 50-500 person company, first CISO hire, founding security engineer, or the CTO who suddenly has "and security" in their job description, and you're being asked for ISO 27001, NIS 2, or SOC 2 with no team, no Big 4 budget, and a deadline approaching, this article is for you.
This is a practical ISO 27001 and NIS 2 readiness playbook for small security teams that need measurable progress, not another spreadsheet.
The path below works. It's been proven by every CISO who has done it, with or without tooling. It assumes you're alone, your time is the bottleneck, and you need to be defensible to an auditor in 4-6 months.
But before the path: a sentence that should reframe how you think about the problem.
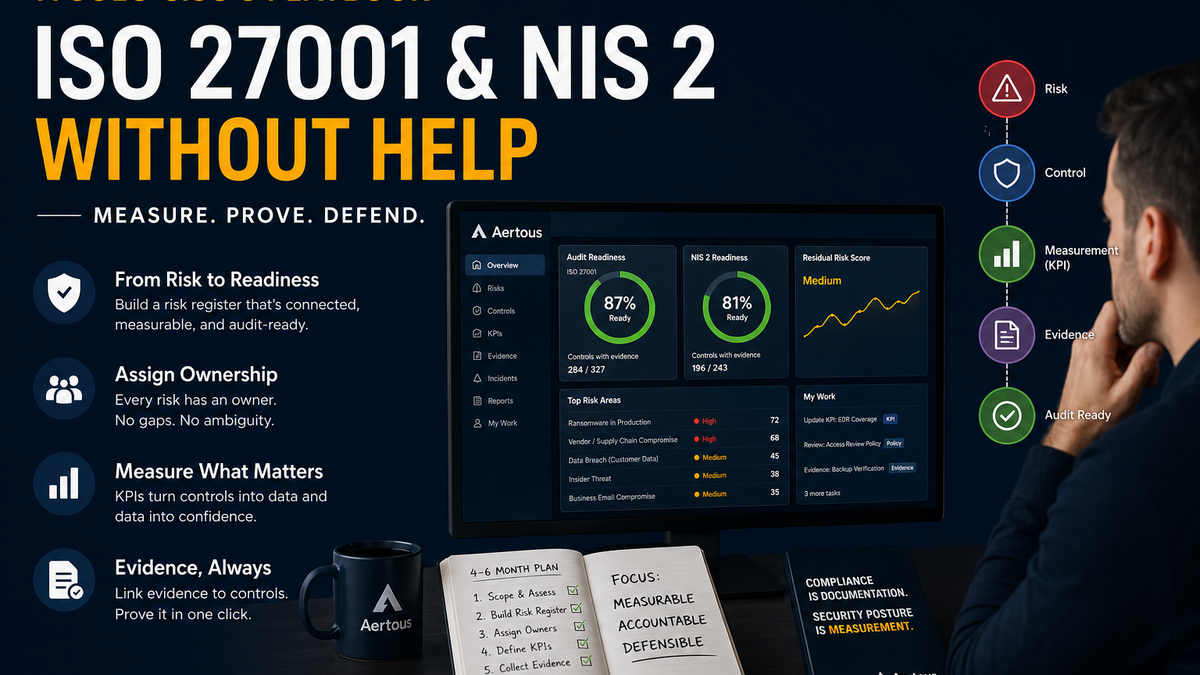
Compliance is documentation. Security posture is measurement.
Most tools sold to solo CISOs are built for the first.
What you actually need is the second.
A documentation tool tells you "you have a policy for X." A measurement tool tells you "the policy for X is being followed, here's the data, here's who owns it, here's the proof." Auditors care about the first; the board cares about the second. CISOs accountable for both need a system built for the second that produces the first as a byproduct.
That's the lens for everything below.
The lie nobody tells solo CISOs about compliance
Every compliance vendor sells "fast." Most of that is marketing.
Real timelines:
- ISO 27001 from zero to certified: 4 to 9 months
- SOC 2 Type 1: 2 to 3 months
- SOC 2 Type 2: 6-12 month observation window
- NIS 2: ongoing readiness with staged incident-reporting obligations, including a 24-hour early warning for significant incidents
No tool changes those timelines. They're set by auditors and regulators, not by you.
What tools CAN compress is everything before the audit:
- Building the risk register (weeks of brainstorming, days of curation)
- Mapping controls to framework requirements
- Assigning ownership
- Collecting evidence
- Knowing where you stand at any moment
If you're solo, that pre-audit work is your single biggest cost. The path below structures it so you don't waste 8 weeks figuring out where to start.
The moment that matters
Not the audit. Not the certification.
The moment your CEO walks in and asks: "Are we exposed right now?"
You either answer in 30 seconds, with data on the screen, with the math to defend the answer.
Or you start opening spreadsheets.
If you cannot answer that question with confidence, the audit is the smaller problem. The audit happens once a year. The CEO question happens monthly. The board question happens quarterly. The breach question, when it comes, decides whether you keep your job.
Compliance work that doesn't make you better at answering these questions is wasted work. Hold every step below to that test.
The mental model: a chain of accountability
Every risk in a defensible security program must connect to:
- A control that mitigates it
- An owner accountable for it
- A measurable signal (objective + KPIs) that proves the control is working
- Evidence that an auditor can verify
Break any link and the chain collapses under audit. Build all four and the program is defensible whether you're solo or have a team of fifty.
Every spreadsheet-based program eventually breaks. Not because spreadsheets are simple. Because they cannot represent these relationships: risk, control, owner, measurable signal, evidence, time. And that's exactly what an auditor tests.
That's not a "tool preference." That's a category fact.
The four-month playbook (week by week)
Day 1: Don't open Excel
The biggest mistake every first-time security leader makes in the first week is downloading the ISO 27001 standard PDF, opening Excel, and starting to type controls.
Don't.
Take three hours and answer four questions on one piece of paper:
- What does the business actually do? (one paragraph, plain English, no jargon)
- What data do we hold? (PII, customer data, financial records, source code, IP)
- Who would attack us, and why? (be specific: ransomware operators, competitor, state actor, opportunistic attacker)
- What's already in place? (existing tools: SSO, EDR, backup, training, MDM, password manager, vulnerability scanner)
This single page becomes the lens through which every later decision happens.
Time: 2-3 hours. Deliverable: One page. Save it. You'll reference it constantly. Common mistake: Skipping the threat model because it feels speculative. Don't. The threat model determines which controls matter.
Day 2-3: Pick your spine framework (and document why)
Most solo CISOs get told they need ISO 27001 AND NIS 2 AND SOC 2 simultaneously. That's the corporate ask. But you can only build one risk register at a time, and 70-80% of controls overlap across frameworks.
Pick one as your spine:
| Spine | When to choose it |
|---|---|
| ISO 27001 | B2B SaaS, global standard your customers will ask about, most flexible mapping |
| SOC 2 Type 1 | North American B2B, fastest first attestation, lighter scope |
| NIS 2 | EU company in a critical sector, the regulator forces your hand |
| NIST CSF 2.0 | Public sector contractor or US-regulated industries |
Document the decision in 2-3 sentences. Show it to the CEO. Their alignment matters when audit time comes and budget is tight.
Time: 2-4 hours including the conversation with leadership. Deliverable: A "why we picked X" memo, ~1 page. Common mistake: Picking the framework the loudest customer is asking about. Pick what fits your actual business.
Day 4-5: Set up your system of record
This is the decision that determines whether you finish in 4 months or 10.
A spreadsheet works for a 10-risk register. You won't have a 10-risk register. ISO 27001 scopes typically have 80-150 risks. SOC 2 has 100+. NIS 2 covers similar ground.
The difference between starting from a blank sheet and starting from a curated, pre-mapped library is the difference between weeks of brainstorming and days of curation.
Most tools optimize documentation. Aertous gives you the operating system underneath it.
Aertous is a CISO Command Center pre-loaded with 540+ risks already mapped to MITRE ATT&CK, NIST CSF 2.0, ISO 27001, and SOC 2. You don't brainstorm risks from a blank page. You triage from a curated library, deploy what's relevant to your stack, customize the org-specific 10-15. What's a 3-week brainstorm exercise becomes a 2-day curation exercise.
The risk register is just the start. Aertous is built around the chain of accountability above: every risk connects to its controls, its owners, its KPIs, its evidence. Documentation is a byproduct of the system, not the goal of it.
Pricing for a typical 50-200 person company runs €199-€649/month. Compare to: 4 weeks of your time at the founder rate, plus likely consultant fees later if you fall behind.
Time: A few hours of evaluation, half a day to set up. Deliverable: Logged into the platform, basic org configuration done. Common mistake: Spending two weeks evaluating tools. The opportunity cost of NOT having a system is higher than picking an imperfect one.
Week 2: Deploy the relevant pre-mapped risks
From the risk library, you triage:
- Definitely relevant (your stack, industry, data): deploy them.
- Probably relevant (adjacent attack paths): deploy with a "review by week 4" tag.
- Definitely not relevant (different industry/stack): skip with a documented reason. Auditors love that paper trail.
- Org-specific risks not in the library: write 5-10 specific to your business.
End week 2 with a starting risk register of 60-100 risks, each tagged for the framework(s) it satisfies. Less than 40 risks: under-scoped, the auditor will catch it. More than 150: over-scoped, you'll burn out maintaining them.
Time: 3-4 days of focused work. Deliverable: Risk register with relevant risks deployed, custom risks added, framework tags applied. Common mistake: Deploying everything "just in case." Maintaining 200 risks badly is worse than maintaining 80 risks well.
Week 3: Assign owners (the difficult conversations)
A risk register without owners is decorative. Auditors catch it in 30 seconds: "Who owns this? Show me their acknowledgment."
For each risk, assign a real human by name. This means actual conversations:
- "Maria, you own ransomware in production." (Maria is your IT lead.)
- "Sales VP, you own customer-data export risk." (They might say "no", that's where leadership alignment matters.)
- "Legal counsel, you own privacy breach response." (External counsel works if internal doesn't exist.)
When a risk has no owner, three options:
- You own it. Acceptable for a few; not for everything.
- The CEO owns it. True for some risks (existential business risk).
- Nobody owns it, but it's accepted. Document the acceptance with date and approver.
In Aertous, the My Work page shows each owner exactly what they're responsible for: their risks, KPIs, pending policy acknowledgments. The CISO doesn't have to chase. The owner opens one screen and sees their queue.
Time: 4-5 days, including stakeholder conversations. Deliverable: Every risk has either a named owner with their acknowledgment, or a documented risk acceptance. Common mistake: Becoming the de-facto owner of every unowned risk. You'll burn out. Push back; document acceptance; escalate to the CEO.
Week 4: Define objectives and KPIs
Each risk needs at least one objective: what does "good" look like?
Example for "Ransomware in Production":
- Objective: 95% endpoint EDR coverage with quarterly verified backups.
- KPI 1: Endpoint-EDR-deployed % (target: 95%, measured weekly, owner: Maria)
- KPI 2: Backup-verification-success % (target: 100% monthly, owner: Maria)
Three rules for KPIs:
- Measurable from data you actually have. Don't pick a KPI you can't get a number for.
- Frequency you can sustain. A "daily" KPI you actually update twice a year is a stale KPI. Stale = zero contribution to your risk score.
- A target that's achievable but stretching. 95% is realistic; 100% is theater.
In Aertous, KPIs feed directly into the residual risk score. As you update KPI values, the score moves. The math is visible, consistent, and easier to defend with auditors and boards.
Time: 3-4 days. Deliverable: Each major risk has 1-3 KPIs with targets, owners, frequency.
Week 5-8: Build the evidence trail as you work
This is the silent compliance-killer for solo CISOs: doing the work but not recording it.
In a spreadsheet world, "I'll write up the evidence pack the week before the audit" becomes hell. You're hunting screenshots, Slack messages, email threads, looking for the version of the policy that was actually approved.
In Aertous, evidence is linked to its control the moment it exists:
- Policy approved, linked to its control with approval date.
- KPI measurement, linked to its risk with timestamp.
- Vendor risk assessment, linked to the third-party-risk control.
When the auditor asks for proof of control X, you click control X. The evidence is there with timestamps and ownership.
The daily Score Coach makes this sustainable. Every morning it generates an insight: what changed yesterday, which KPIs missed target, what to focus on. You don't hunt for the state of your program, it's the first thing you read with your coffee.
Time: 30-45 minutes daily. Deliverable: By week 8, your major controls have at least one linked evidence item with a recent date. Common mistake: Treating evidence as something to do "later." Later doesn't come; the audit comes instead.
Week 9-10: Gap analysis (face the truth)
Audit Readiness review:
- For each framework, what % of controls have linked evidence?
- For each risk, does it have an owner and at least one KPI?
- Which KPIs are stale?
- Which controls are marked compliant via override (and is the justification clean)?
Aertous's Audit Readiness widget shows per-framework progress in real time. Each percentage is "controls with linked evidence / total controls × 100", actual math, not a vibe.
Output: a prioritized gap list. Sort by:
- Required for spine framework
- High-risk gaps (critical risks with no owner or measurement)
- Easy wins (10-minute fixes)
- Long-tail (low-priority controls)
Time: 3-5 days. Deliverable: Gap remediation plan with target dates.
Week 11: Close priority gaps
Heads-down execution. Each gap is a specific task: write a missing policy, deploy an unowned KPI, document a status override, get an approval signature.
By end of week 11, your Audit Readiness % should be 85%+ on your spine framework.
Week 12: Pre-audit dry run
Self-audit against your spine framework. Walk through each control as if you're the auditor:
- "Show me your evidence for control 8.5" → Click. Time the answer. Should be under 30 seconds.
- "Where's the policy approval audit trail?" → Click. Should be visible.
- "Who is the risk owner for risk Y?" → Click. Name with recent acknowledgment.
If anything takes more than 2 minutes to find, you have a structural problem. Fix it before the auditor arrives.
Month 4-5: Audit window
Schedule the auditor. For ISO 27001 you'll need an accredited certification body, book 6-8 weeks ahead. Stage 1 audit reviews documentation. Stage 2 reviews implementation.
Most auditors will issue 5-15 minor findings on a first audit. Major findings are rare if you've prepared.
Month 5-6: Certification
Close findings within the auditor's deadline (usually 90 days). Address each, link new evidence, schedule follow-up review. Final certificate issued.
Total: 4-6 months from zero to certified, solo, without Big 4 consultants.
Compare to the typical pattern: do nothing structured for 4 months, panic-prep for 2 months, fail the first audit, hire consultants for €30-50k, eventually certify in month 9-12.
The expensive choice is doing it slowly with the wrong tooling.
What about NIS 2 specifically
NIS 2 differs from ISO 27001 in three ways:
- Regulation, not certification. No formal audit; you self-attest. But if there's an incident, the regulator can demand evidence retroactively.
- Staged incident-reporting obligations: a 24-hour early warning for significant incidents, a 72-hour incident notification, and a final report later.
- Strict penalties in EU member states for non-compliance.
NIS 2 doesn't ask if you have a process. It asks if you can prove what happened, within 24 hours of detection.
This is where defensibility stops being abstract. A regulator showing up after an incident is the question-after-the-breach moment, with a deadline. If your incident logging is in Slack threads and email, you're going to fail that question even if your underlying response was technically sound.
The work overlaps massively with ISO 27001: risk management, incident response, business continuity, supply chain security. If you've done ISO 27001 properly, NIS 2 is 70% there. The 30% that's NIS 2-specific:
- Provable incident timeline (24h early warning, 72h notification, final report)
- Supply chain risk depth
- Board accountability for cybersecurity
In Aertous, incidents get logged with timestamps the moment they're discovered. The 24-hour clock starts on the timestamp, not on a Slack thread. Each decision made during response (containment actions, communication, escalation) is recorded with the actor and the time. When the regulator asks "what happened and when?" the answer is a click, not a reconstruction.
So if you're using Aertous for ISO 27001, you're 70% of the way to NIS 2 evidence.
What Aertous won't do for you
Honest list:
- Not an EDR. You still need CrowdStrike, SentinelOne, Microsoft Defender.
- Not a SIEM. You still need Datadog, Splunk, or similar for log aggregation.
- No automatic evidence collection from external tools today. Manual linking. Auto-collection is on the Q4 2026 roadmap.
- Not the auditor. Aertous makes the audit go faster. It doesn't replace the certification body.
- No published case studies yet. Aertous is a 2026 company. We won't fabricate references.
What it does is the thing that takes the most CISO time and the fewest CISO-uniquely-skilled hours: maintaining a live, defensible, queryable system of record.
A test you can run in 30 minutes, today
Open a blank document. Don't open Excel. Don't open Aertous. Just paper.
Write the first 10 risks you'd put in your risk register, by name.
For each, in one line, fill out:
- Risk name
- Who owns it
- One measurable signal (KPI) that would prove it's controlled
- Where the evidence lives today
You'll find one of three things:
- You can fill it out in 30 minutes. You're further along than you think. Now you need a system to operationalize it. Skip the next 4 months of confusion.
- You can fill out 5 of 10 but stall on the rest. That's normal. You have a starting point. Now you need a curated library to fill in the gaps without 3 weeks of brainstorming.
- You can't fill out any. That's also normal. You don't have a tooling problem. You have a system problem. Aertous gives you the system, not just another tool.
If you're in case 2 or 3, and most solo CISOs starting from zero are, that's exactly what Aertous is built for.
Book a 30-minute walkthrough at aertous.com/request-trial.
We'll work through your first 10 risks together. If Aertous fits, you leave with a deployable starting register. If it doesn't, you still leave with a methodology you can run anywhere.
You don't fail ISO 27001 because you didn't work hard enough.
You fail because your system cannot prove the work you already did.
Fix the system, and the audit becomes a review of work already proven.
Compliance is documentation. Security posture is measurement. Aertous is built for the second.
Written by cybersecurity practitioners building the posture management platform for modern teams.